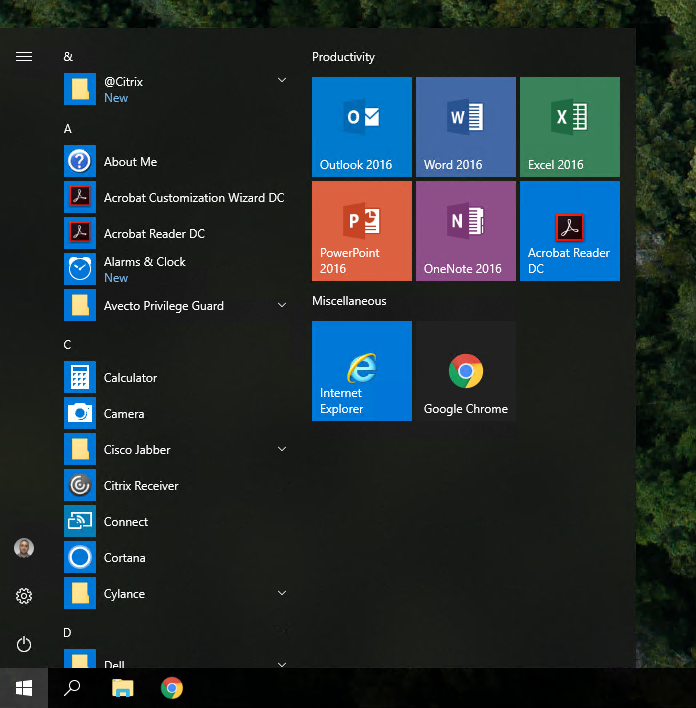
I have noticed recently that some users that have upgraded from 1607 to 1709 have lost their Start Menu tiles during the upgrade. I did a lot of research on the Start Menu topic and could only find one article from Microsoft stating that they were replacing the TileDataLayer feature with something called the TileStore. You can see the list of features that are removed or deprecated in Windows 10 Fall Creators Update here.
I’m suspecting that there is an issue migrating the tiles to this new feature and it is causing the start layout to become corrupt during the upgrade for some users. I even have a ticket open with Microsoft concerning this issue but unfortunately it does not look like it will be fixed anytime soon.
So here is my workaround and hopefully it can help someone else.
First you will need to make sure to export every user’s start layout. I am doing this with a scheduled task that will run the following Powershell command:
Export-StartLayout –path $env:LOCALAPPDATA\LayoutModification.xml
This will export the user’s existing start layout and it will copy it to their %LOCALAPPDATA% folder.
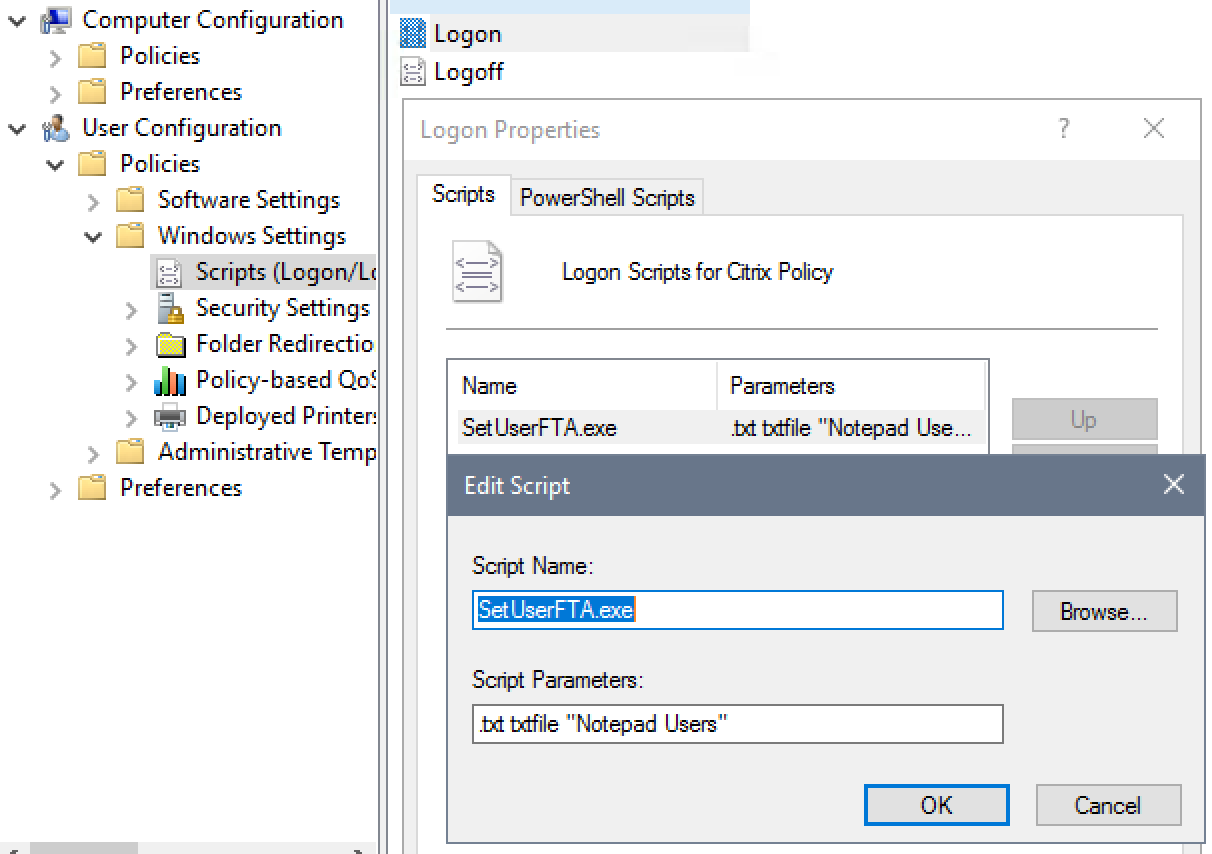
Once you have given the scheduled task enough time to export everyone’s start layout, you can start the upgrade and run the following script at logon to bring back the user’s customized start layout:
If((Test-Path $env:LOCALAPPDATA\LayoutModification.xml) -eq $True) {
Copy-Item $env:LOCALAPPDATA\LayoutModification.xml $env:LOCALAPPDATA\Microsoft\Windows\Shell\LayoutModification.xml -Force
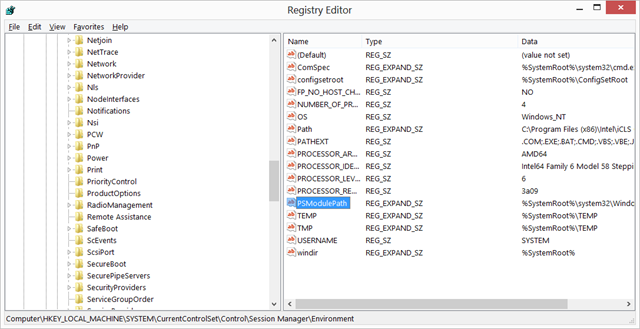
Remove-Item 'HKCU:\Software\Microsoft\Windows\CurrentVersion\CloudStore\Store\Cache\DefaultAccount\$start.tilegrid$windows.data.curatedtilecollection.root' -Force -Recurse
Get-Process Explorer | Stop-Process
}
Note: If you are experiencing this issue with 1809, you can run the following script to bring back the user’s customized start layout:
If((Test-Path $env:LOCALAPPDATA\LayoutModification.xml) -eq $True) {
Copy-Item $env:LOCALAPPDATA\LayoutModification.xml $env:LOCALAPPDATA\Microsoft\Windows\Shell\LayoutModification.xml -Force
Remove-Item 'HKCU:\Software\Microsoft\Windows\CurrentVersion\CloudStore\Store\Cache\DefaultAccount\*$start.tilegrid$windows.data.curatedtilecollection.tilecollection' -Force -Recurse
Get-Process Explorer | Stop-Process
}